
People's Republic of China Cyber Threat
CISA works to ensure U.S. critical infrastructure, government partners, and others have the information and guidance to defend themselves against Chinese State-Sponsored cybersecurity risks.
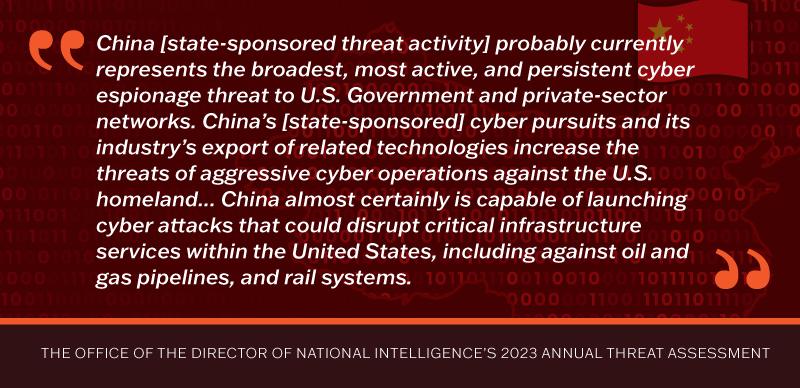
CISA has long been concerned about the breadth, depth, and sophistication of the People's Republic of China (PRC) state-sponsored cyber threat to the United States, and we have worked to ensure U.S. businesses and government agencies have information and guidance to defend against those risks.
Every organization must take urgent action to understand and address known tactics, techniques, and procedures used by PRC state-sponsored cyber threat actors – including efforts to detect and prevent intrusions and respond to and recover from incidents, particularly by investing in the operational resilience of essential services.

CISA Live! Presents: “People’s Republic of China Cyber Threats and What We Can Do”
Join us on May 15 at 11:30am EDT for our next CISA Live!. Andrew Scott, CISA’s Associate Director for China Operations, will discuss why cyber actors from the People’s Republic of China pose a significant threat to U.S. critical infrastructure.

Living off the Land
This Advisory focuses on a set of techniques, called "living off the land," used by cyber actors to maintain anonymity within IT infrastructure by abusing tools already present in the environment such as PowerShell, WMI, and FTP clients. Also see the accompanying fact sheet.

CISA and Joint CISA Publications
Review China-specific Alerts and Advisories here.
To improve your cyber resilience against these threats, start here:
CISA and our partners in the U.S. government and around the world provide timely and actionable information about the PRC state-sponsored cyber threat to help organizations prioritize the most effective cybersecurity measures.

- Assess your organization’s current security posture and implement Cybersecurity Performance Goals (CPGs) to bolster resilience.
- Establish a baseline normal host behavior and user activity to detect anomalous activity on endpoints when reviewing logs. See CPG 2.T: Log Collection and CISA's free Logging Made Easy, CISA's open-source log management solution for Windows-based devices.

- Prioritize mitigation of Known Exploited Vulnerabilities, including those outlined in our joint advisory on the top Common Vulnerabilities and Exposures (CVEs) used since 2020 by PRC cyber actors.
- Prioritize logging (e.g., command-line interface "CLI") and close and/or monitor high-risk ports (e.g., Remote Desktop Protocol, Server Message Block, File Transfer Protocol, Trivial File Transfer Protocol, Secure Shell, and Web Distributed Authoring and Versioning).
- Isolate privileged administrator actions and locations to a manageable subset of locations, where effective baselines of “where” and “who” can be established. See CISA and NSA's Identity and Access Management Recommended Best Practices Guide for Administrators for guidance on establishing the principle of least privilege.

Urgently report potential malicious activity to CISA or the FBI:
- The easiest way is to go to CISA.gov and click the “report a cyber issue” button right up top.
- You can also contact CISA’s 24/7 Operations Center: cisa.gov/report | report@cisa.gov | 888-282-0870
- Contact your local FBI field office or IC3.gov.

Establish a relationship with a regional CISA Cybersecurity Advisor to access additional services, assessments, and guidance.

- Sign up to receive CISA’s cybersecurity alerts and advisories for timely notification of emerging campaigns and incidents. Review earlier advisories on PRC cyber threats. CISA particularly recommends reviewing China-specific advisories.
- Sign up for CISA’s free Vulnerability Scanning service to receive early warning when a vulnerability known to be exploited by PRC cyber actors or other malicious groups are identified on Internet-facing assets.

Watch CISA Director Easterly Testify Before the House Select Committee on the CCP
CISA Director Easterly testifies during a January 31, 2024 congressional hearing on PRC state-sponsored cybersecurity threats.
Key Resources

Defending Against Nation-State Cyber Threats
Find more information on Nation-State adversaries and related resources.

CyberSentry Program
This threat detection and monitoring capability for IT and operational technology provides persistent visibility into adversary activity targeting critical infrastructure networks and can drive urgent mitigation where activity is identified.
Blogs

Blog: Under the Digital Radar: Defending Against People’s Republic of China’s Nation-State Cyber Threats to America’s Small Businesses
For years, CISA has worked to defend federal, state, local tribal, and territorial governments as well as our private sector partners from malicious cyber activities emanating from the People’s Republic of China.



